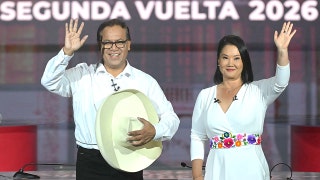
The website of the Syrian Electronic Army, a shadowy, pro-Assad group which has orchestrated cyber attacks on President Obama and Oprah's Facebook pages.
The security forces of President Bashar Assad has moved ahead on multiple fronts. An estimated 10,000 people have been arrested and there are reports that some dissidents have been tortured to reveal their Facebook passwords. Foreign journalists have been banned from entering the country and access to the Internet and the mobile phone network has been curtailed.
Meanwhile, a shadowy group calling itself the Syrian Electronic Army (SEA) has orchestrated an array of cyber attacks in three key areas: spamming popular Facebook pages, such as President Barack Obama, the U.S. Department of State, French President Nicolas Sarkozy and Oprah Winfrey with pro-Assad propaganda; defacement attacks against Syrian opposition group websites, and defacement of Western websites.
“It’s the first case of an open, organized and orchestrated pro-government web attack group with a public presence on a national network in the Arab world,” explained Helmi Noman, a senior researcher with the OpenNet Initiative, a collaborative partnership between the Citizen Lab inside the Munk School of Global Affairs at the University of Toronto, the SecDev Group in Ottawa and the Berkman Center at Harvard University.
Noman, who’s been documenting the cyber activities of the SEA, also known as Syrian Electronic Soldiers, told Fox News the group claims to be separate from the government – a group of independent young people who claim to love their country and are launching electronic counterattacks against those people and groups allegedly attacking Syria.
Noman disputes that claim.
“What we were able to reveal is that the SEA’s website domain name was registered by the Syrian Computer Society (SCS), an organization headed by Syrian President Assad in the 1990s before he assumed the country’s presidency,” Noman told Fox News. The president late brother, Bassel Al-Assad, founded the SCS in1989, according to Noman.
Ron Deibert the director of the Citizen Lab told FoxNews.com the SEA operates on the Syrian national Internet network, which means “it has the tacit approval of the Syrian government.” Plus, he added, “its exploits are also being applauded by the state-controlled media in that country.”
Deibert also told FoxNews.com the SEA is following the playbook used in Iran by the Iranian Cyber Army to disrupt, distort and deny service to opposition sites.
The Citizen Lab, he said, has been tracking the apparent support given to the SEA by the Iranians including software designed to spam, deface, hack and track websites and Facebook pages of groups and individuals perceived as threats to the ruling order.
Ironically, Deibert said one of the software programs reportedly being used in the Middle East against pro-democracy groups and dissidents is Finfisher, a web exploitation kit, jointly produced by firms in the United Kingdom and Germany.
The activities of the SEA, Deibert said, have also included “man in the middle” spoofing which produces phony certificates which are used to authenticate legitimate websites before users sign on to them. These phony certificates have enabled groups like the SEA to collect passwords and IP (Internet Provider) addresses of the users who perceived to be opponents of the regime.
Noman told Fox News that the SEA has not only been disrupting and defacing other websites and Facebook pages, it also has been setting up its own Facebook pages to brag about its cyber exploits, promote its “patriotic” support for the Assad government and point people to sites where they can download hacking software.
But those pages, Noman said, have been shut down by Facebook almost as quickly as they’ve been put up. At last count, he said, Facebook has shut down 29 pages put up by the SEA. The most recent shut down of a SEA page – www.facebook.com/syria.28 -- came Wednesday after Fox News contacted Facebook about the pages.
In response to the FoxNews.com inquiry, a Facebook spokesperson said, “Nothing is more important to us than the security of the people who use Facebook. We continue to investigate these reports and, if they are confirmed, will take appropriate action to protect our users.”
The Facebook spokesperson declined to discuss the specific reasons for taking down the SEA pages. However, the presumed reason is the SEA’s alleged violation of the terms of service agreement that all Facebook users must follow.
Facebook’s shutdown of their pages have spawned accusations by the SEA and by state-controlled Syrian media that the company was “conspiring against the Syrian people” and practiced “double standards” by permitting pages calling for a so-called Syrian revolution.
The Facebook spokesperson declined to comment on these charges.
Another aspect of the SEA activities has been the hacking and defacing of opposition websites and presumably the collection of dissident IP addresses.
Abdullah Rifai, a spokesman for the Virginia-based pro-democracy group the Syrian Emergency Task Force which recently filed a federal lawsuit against the Syrian government for alleged human rights violations told FoxNews.com his group was very aware of the SEA activities and believes they have been attacking his group’s site.
“Ever since we began we have experienced attacks against our web page, our email and our servers but none of them have succeeded because we have very strong security protections.”
Rifai said his group has also tracked the IP addresses of many of the presumed attackers and found that almost all of them are based in Syria, China and Russia.
That doesn’t surprise Eric Rosenbach, of the Virginia-based Good Harbor Consulting, a global security and risk management firm led by Richard Clarke, former White House senior advisor to Presidents Clinton and Bush.
“Most of the leading cyber crime activities today are being run or controlled by Russian and Chinese organized crime syndicates,” Rosenbach told FoxNews.com. “So it would make sense for the Syrians to hire them as proxies to do their dirty work thereby giving them plausible deniability.”
The only problem, said Rosenbach and Deibert, is differentiating between what is your “run of the mill” criminal cyber activity from what are political cyber-attacks.