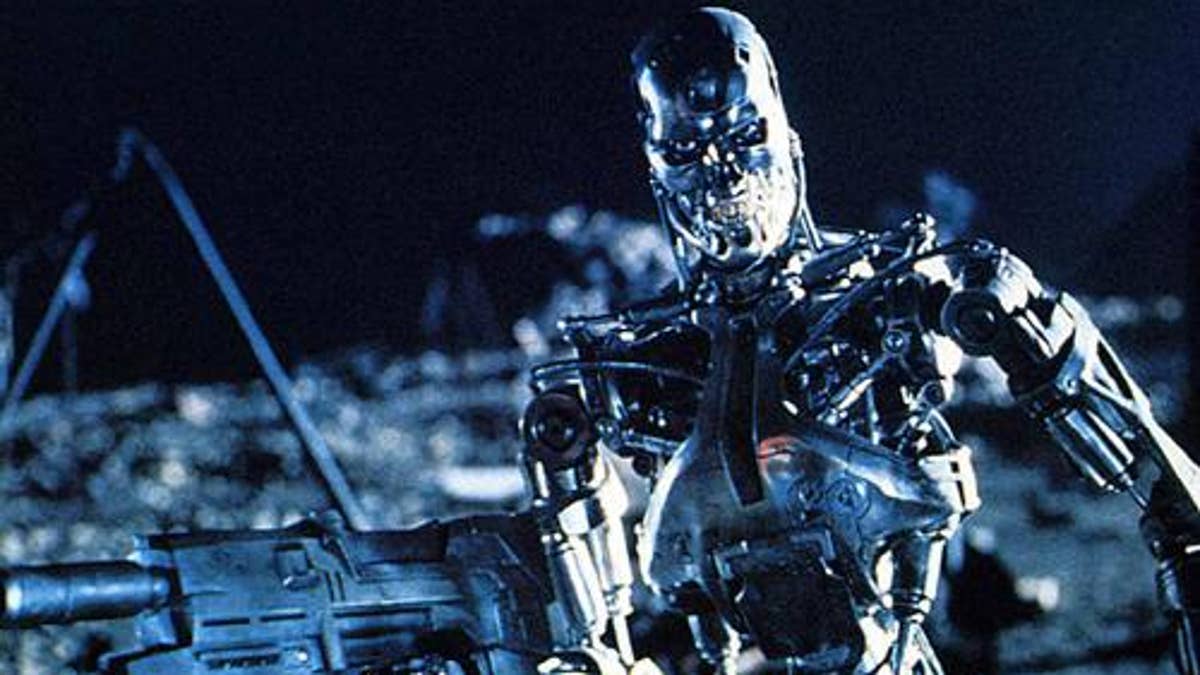
(Orion Pictures)
In your favorite crime drama, the heroine studies a video from a store surveillance camera. It's dark and grainy, and the people on the screen can barely be distinguished from the background.
"Can you clean that up?" she asks.
"Sure," says the computer tech. After a few keystrokes, the photo is clear as a bell.
"Zoom in," says the heroine. The tech zooms into the image and presto, we can clearly read the suspect's name stitched right on his shirt. Case closed.
Could this happen in real life? Not even close. Try that enhance-and-enlarge scenario in real life, and you'll end up with an image that's nothing but a blocky mess!
Unfortunately, many "high-tech" scenes in TV shows and movies are simply laughable -- especially because entertainment that incorporates real technology in the right way is so much more engaging.
Another Hollywood "favorite" of mine is when hackers break into government servers seemingly by magic. Sure it's possible, but it takes unbelievable time, skill and effort -- not a few minutes while a bomb timer is ticking away. Plus, most hackers would use a phishing attack instead of tackling a government firewall directly.
Of course, some seemingly improbable tech dangers are very real. A TV show or feature film can get it right, and the viewer might still think it's made up.
Some of the most popular movies of recent years have some of the most ridiculous tech scenarios. I won't even address the obvious abusers, such as The Matrix and the Terminator series. But consider a few I find humorous:
* Sneakers: Robert Redford's team cracks any password with a gadget that looks like a 1990s answering machine.
* Swordfish: Hugh Jackman hacks into a sophisticated government computer in seconds - while a gun is held to his head, among other distractions.
* War Games: A very baby-faced Matthew Broderick hacks into a NORAD computer from his 1980s bedroom.
* Independence Day: Jeff Goldblum and Will Smith successfully communicate with an alien computer and upload a virus to save the world -- and they're using a Mac. Right. The Macs in our office still can't communicate with the printers half of the time.
* 2001: A Space Odyssey: Dave is able to use voice commands to perfection, never repeating a word and with no misinterpretation. It's 11 years past that science-fiction date, and the telephone company's voice recognition software still can't get me to a live rep.
Now it's your turn. See if you can detect what's wrong with the tech in this recently written plot:
* A detective finds a sniffer attached to the back of his computer to track his movements, so he removes it and hands it over to the police.
Could this happen?
No. A sniffer can be either hardware (a highly specialized computer) or software (a program installed on a regular computer). It's the nickname for a packet- or network-analyzer. It monitors traffic on a network and can be used by hackers. But it's not something you remove and hold in your hand once finding it stealthily attached to the back of your computer.
What should it have been? If it were my book, I'd make it a hardware keylogger. If you unplug the computer's keyboard and stick the keylogger into the keyboard's port, you can then plug the keyboard into the keylogger. It would be very hard to spot, because they're very small. Plus, the keyboard usually plugs in at the back of the computer. It can be physically removed, and could be turned over to the police. Plot problem solved.
So, next time you watch a crime drama, be a tech detective yourself, and see if they get it right. And help keep Hollywood honest.
Kim Komando hosts the nation's largest talk radio show about consumer electronics, computers and the Internet. Get the podcast or find the station nearest you at www.komando.com/listen. Subscribe to Kim's free e-mail newsletters at www.komando.com/newsletters. Copyright 1995-2012, WestStar TalkRadio Network. All rights reserved.







































