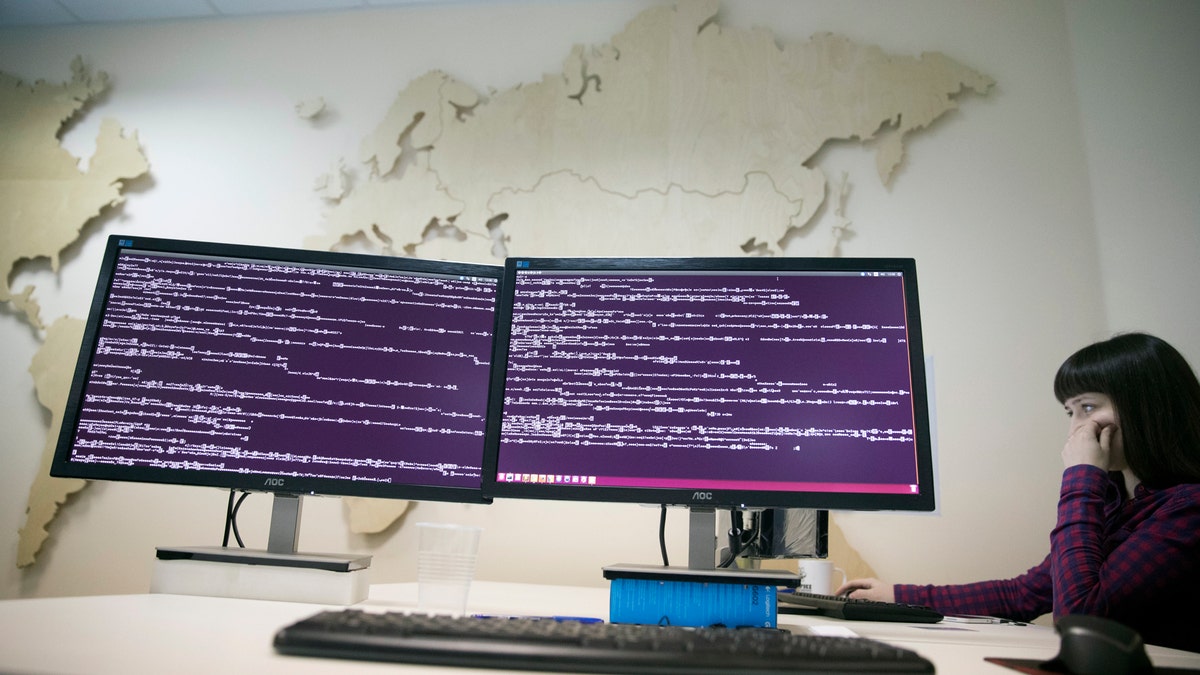
A computer code is seen on displays in the office of Global Cyber Security Company Group-IB in Moscow, Russia, Wednesday, Oct. 25, 2017 as reports emerge of new ransomware dubbed 'Bad Rabbit.' (AP Photo/Pavel Golovkin)
Networks in Russia and Eastern Europe have been targeted by a new strain of ransomware dubbed 'Bad Rabbit,' a possible variant of the 'Petya' malware that hit computer systems earlier this year.
Bad Rabbit, which appears to have originated in Ukraine, hit computers at the Odessa international airport in southern Ukraine and the Kiev subway. Prominent Russian media outlets such as Interfax and Fontanka also reported being targeted Tuesday.
The Moscow-based cybersecurity firm Group-IB said Wednesday the ransomware also tried to penetrate the computers of major Russian banks but failed. None of the banks has reported any attacks, though the Russian Central Bank said Wednesday it had recorded BadRabbit's attack on its systems but they were not compromised.
HUGE 'PETYA' RANSOMWARE ATTACK HITS EUROPE, SPARKS MASS DISRUPTION
Cybersecurity specialist Kaspersky Lab, which is based in Moscow, describes Bad Rabbit as a “drive-by” attack. “Victims download a fake Adobe Flash installer from infected websites and manually launch the .exe file, thus infecting themselves,” it said, in a statement. Kaspersky Lab reported that the criminals behind Bad Rabbit are demanding 0.05 bitcoin as ransom, roughly equivalent to $280.
While most of the ransomware’s victims have been in Russia, Kaspersky Lab also noted attacks in Ukraine, Turkey and Germany.
Prague, Czech Republic-based cybersecurity firm Avast Software reported late Tuesday that Bad Rabbit had been detected in the U.S. "We expect a growing number of detections in the hours ahead," it tweeted.
Bad Rabbit is a suspected variant of the recent ‘Petya’ ransomware that sparked disruption across Europe, according to a number of experts, including the U.S. Computer Emergency Readiness Team (US-CERT). “US-CERT discourages individuals and organizations from paying the ransom, as this does not guarantee that access will be restored,” it said in a post on Tuesday.
PETYA RANSOMWARE: EXPERTS TOUT 'VACCINE' TO PROTECT COMPUTERS FROM CRIPPLING CYBER ATTACK
Experts warn that organizations across the globe should be on their guard against Bad Rabbit. “As businesses in Russia and Ukraine report infections, global companies must look inward and ask themselves, ‘Have I done enough? Did we patch our systems after Petya? Have we shored up our perimeter web and email defenses?’” Steve Malone, director of security product management at email security specialist Mimecast explained in an email to Fox News. “History tells us the answer to these questions is very likely no, so once again, brace for further widespread outbreaks.”
“Ransomware is cheap to make and lucrative when it works, so we can expect to see a lot more of it,” noted Shirali Patel, cybersecurity manager at defense and cybersecurity specialist Raytheon, in an email. “While reports indicate Bad Rabbit is affecting networks primarily in Russia and eastern Europe, we know how easily malware can jump from one host to another.”
“For organizations to effectively defend against attacks like Bad Rabbit, they need to have instant visibility into which of their assets are susceptible to the attack,” added Manoj Asnani, vice president of product and design at security specialist Balbix. “On-tap visibility is very hard to achieve manually. Security teams must have automated systems in place that can continuously monitor these type of attack vectors and provide vital information instantly when needed.”
AFTER NSA TOOL USED IN PETYA CYBERATTACK, CONGRESSMAN URGES AGENCY TO THWART MALWARE
Bad Rabbit has emerged just four months after Petya, which itself came hot on the heels of the WannaCry ransomware that wreaked havoc across the globe.
The scale of the ransomware threat was highlighted last year when a Los Angeles hospital paid nearly $17,000 in bitcoins to hackers who disabled its computer network.
However, Bob Rudis, chief data scientist of cybersecurity specialist Rapid7 does not think that Bad Rabbit will hammer U.S. organizations. "Enough awareness has been raised and researchers have identified a number of ways to prevent the attack from
occurring that it is unlikely we'll see significant growth," he explained, via email. "As of now, BadRabbit has been contained to the original target regions, with a few confirmed infections in the U.S., but these appear to be rare."
The Associated Press contributed to this article.
Follow James Rogers on Twitter @jamesjrogers







































