Could Iran-US cyberwar lead to physical war?
Could Iran-US cyberwar lead to physical war? Heritage Foundation's Lt. Col James Carafano weighs in on Iran’s cyberwar with the United States
In the aftermath of last month's Saudi oil field attacks, believed to have been carried out by Iran, cybersecurity experts have detected an uptick in Iranian movement — and they contend it aims to both guard their nation against retaliation and to launch its own attacks in the shadowy arena of cyberspace.
“Both the U.S. and Iran are maneuvering in this space right now, and we will see ongoing attacks from both sides. The key question is how far will they go and how much the situation escalates,” David Kennedy, founder and CEO of TrustedSec and a former U.S. military intelligence analyst told Fox News. “Iran has been aggressive over the past several years when it comes to cyberattacks. Its back is against the wall, and it has less to lose from a cyberwar with the United States.”
President Trump has long expressed his hesitation for the Islamic Republic of Iran. The country has remained at the forefront of his foreign policy decisions, subject to both economic and military threats. Nonetheless, Trump has also advocated for getting the U.S out of the Middle East and becoming further embroiled in protracted conflicts – making cyberattacks and digital warfare effective and clean-handed methods to cripple Tehran further and demonstrate American strength.
“Iran is currently preparing for an attack and seems to be slowing their current attacks as a matter of readiness,” said Jeff Bardin, chief intelligence officer at cybersecurity firm Treadstone 71. “All critical infrastructures are moving to higher readiness levels.”

In this photo opportunity during a trip organized by Saudi information ministry, a man watches the damaged in the Aramco's Khurais oil field, Saudi Arabia, Friday, Sept. 20, 2019, after it was hit during Sept. 14 attack. Saudi officials brought journalists Friday to see the damage done in an attack the U.S. alleges Iran carried out. (AP Photo/Amr Nabil)
Information intercepted by Treadstone 71 in recent weeks shows that Iran has summoned its critical forces and facilities at an “orange” level of preparedness urgency, issuing orders to gas refineries, petrochemical projects, and complexes, terminals, health facilities, and oilfields.
Orange level, according to experts, refers to the “high probability” hazard. The order letter was published in the days after the Saudi oil field attack by Iranian news agency Ilna, but the document was promptly deleted.
A number of petrochemical websites have been determined to be already comprised, Treadstone analysts reported, but it remains to be seen exactly how and by whom. Netblocks have also recorded, in recent weeks, several network and Internet disruptions in both Iran’s public and industrial sectors.
However, unleashing the brunt of cyberweaponry isn’t without blowback and consequences. In recent years, Iran has emerged as one of the world’s most potent global forces in cybersecurity.
“Iran may have cybercapabilities to disrupt Gulf State and Saudi facilities to further drive up the price of oil. And Iran has been working for several years to build their national Internet under the protection of their ‘Chinese firewall’ named Dezhfa,” Bardin said. “They also have been working to push their own versions of social media programs trying to prohibit or greatly limit access to Facebook, Telegram, Twitter, and Instagram, to name a few.”
Tehran is said to be pushing these apps via the IRGC-funded Café Bazaar, their version of Google Play store.
“They are looking to build their own cellphones but realize that the Android operating system will still come with vulnerabilities regardless,” Bardin said. “They have focused on the petrochemical, energy, and financial sectors but admittedly have not spent a great deal of time on other areas including biohazards, food, and water supplies.”
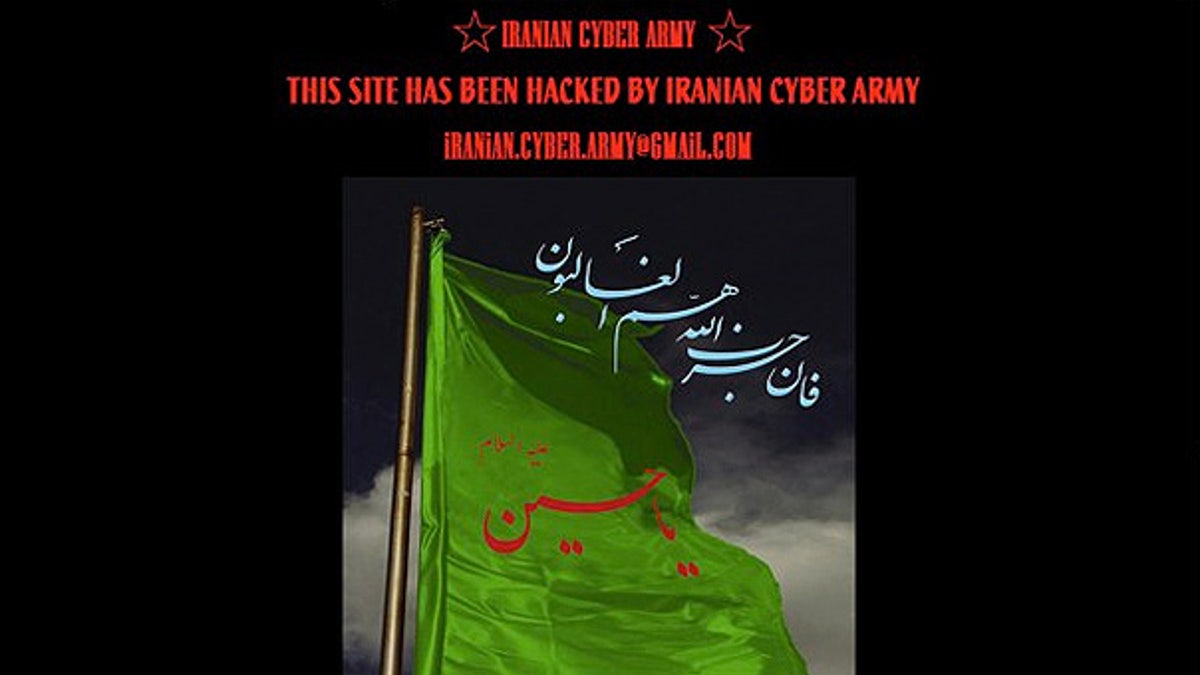
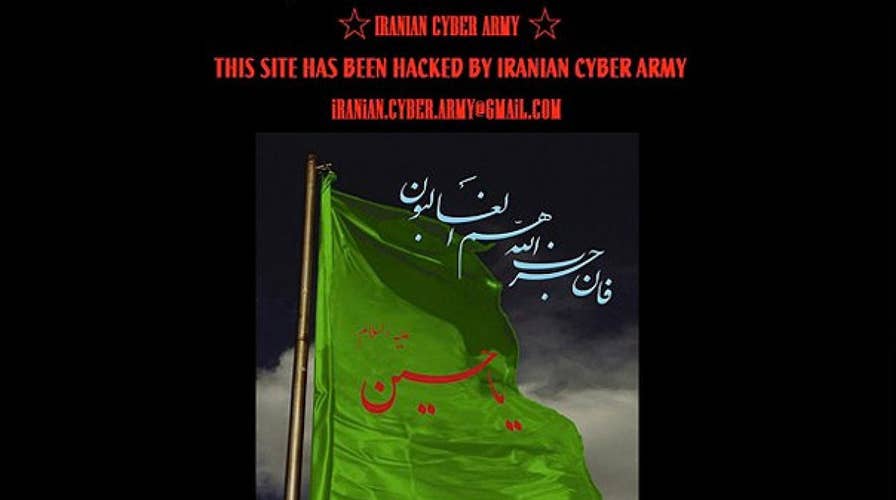
Dec. 18: A screenshot of Twitter.com shows the site defaced by a group calling itself the 'Iranian Cyber Army.'
Moreover, for years Iran has been preparing cyberbattalions – made up of regular citizens – and now boasts thousands of them, using the same strategy used in the Iran-Iraq war of the 80s — that is, focusing in the sheer number of "soldiers" involved, Bardin highlighted. During that war, Iran used "cheaper" resources to clear minefields, that being the Basij militia. Today, they seem to be following the same methodology while protecting the Islamic Revolutionary Guard Corps (IRGC) and highly trained cyber special forces for critical cyber combat roles.
And while the cyberspace may seem bloodless, experts also underscored that a cyberattack could inflict more damage immediately than military action.
“Casualty loss is definitely the largest potential for cyberwar. Shutting down critical systems can have an absolute impact on loss of life,” Kennedy observed. “Additionally, if the operators are not planning the attack correctly, there could be potential for attacking the wrong targets and not having a full understanding of the systems that they are in.”
Over the weekend, Iran’s Oil Minister Bijan Zanganeh, further warned the petroleum industry – via the ministry’s news agency SHANA – to remain vigilant to cyberattacks as tensions with the U.S., Saudi Arabia, and other adversaries continue to proliferate.
The cyberattacks launched from either side typically occur through phishing or social engineering, experts noted, by finding a flaw in their target’s infrastructure and using that to gain access into sensitive systems.
“You could do anything from shutting down oil production to shutting down power, disabling military capabilities, crippling the financial sector, and more,” Kennedy explained.
After Iran was accused of downing a U.S. drone in June, Trump initially sought to respond with a military strike. He called it off at the eleventh hour and instead opted for a series of cyberattacks against Iranian computer apparatuses.

Israel's legendary spy agency, the Mossad, has long been suspected of having a hand in the Stuxnet computer worm that wreaked havoc in Iran's nuclear program in 2010. (Reuters)
A decade ago, the U.S. and Israel teamed up to clandestinely impair Iran's nuclear program with the Stuxnet computer virus, bringing down the centrifuges known to be enriching uranium. While Tehran kept relatively quiet on the matter, experts have speculated over the years that they used the information gathered from that attack to create the virus “Shamoon,” which they first used in 2012 against Saudi Aramco and then in another attack wave in 2017.
CLICK HERE FOR THE ALL-NEW FOXBUSINESS.COM
Heather Heldman, a former advisor at the U.S. State Department and now managing partner at the Luminae Group, a geopolitical intelligence firm, also highlighted that if cyberattacks headed by the United States become routine, “we risk normalizing this type of activity and losing the element of restraint that has generally prevailed between nations in times of high tension to date.”
“Such a change would pose an enormous threat to U.S. businesses and infrastructure,” she added. “And depending upon how Iran perceives its own cyberdefenses, it may be preparing its proxies to respond in more conventional ways should it sense that it has been the victim of a successful cyberattack.”