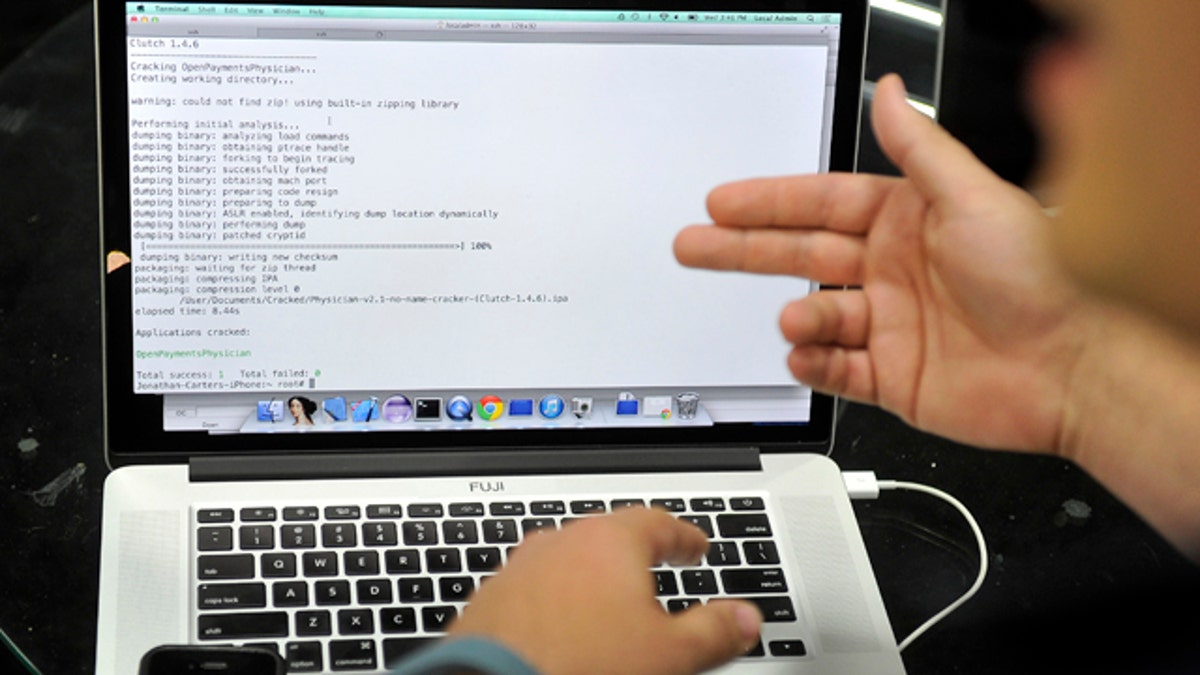
August 6, 2014: Joe Abbey, Arxan Technologies' director of software engineering, displays on his computer how he hacked into a phone app during a demonstration at the Black Hat USA 2014 cyber security conference, in Las Vegas. (AP)
Weeks before the State Department’s Nov. 16 shutdown of its unclassified email system in the face of unprecedented hacking attacks, auditors took the department’s management to task for ignoring warnings about their lax security habits and chronic failure to enact protections against high-tech intruders.
The situation was so bad, the auditors say in a highly censored report, that they “identified control deficiencies across a total of 102 different systems reviewed over five years, yet many of the same deficiencies have persisted.”
State Department bureaucrats say that they are working to fix the problems — even as the document notes that that the same problems were identified a year ago or longer.
The State’s bureaucracy disputes the audit’s finding that State’s info-tech weaknesses amount to a “significant deficiency” in its security, defined as a weakness that “significantly restricts the capability of the agency to carry out its mission or compromises the security of its information, information systems, personnel, or other resources, operations, or assets.”
Instead, State Department Chief Information Office Steven C. Taylor says that “in a changing business environment of the Department's size and geographic dispersion, we expect to encounter challenges on a regular basis,” and that “we have created a foundation for correcting several existing weaknesses and an ability to address new issues as they arise.”
One of the key findings of the audit, however, is that no matter what the diplomats say, State’s lack of response to repeated warnings about its security failings “has been a perennially recurring problem across many Department systems and is undoubtedly systemic in nature.”
Moreover, as the audit notes in a diplomatically buried footnote, the State Department’s Inspector General’s Office has been reporting lapses in the bureaucracy’s handling of “risk management” of security issues since 2010. And “many of the same deficiencies remained uncorrected in [fiscal year] 2014."
Just how systemic the deficiencies are is not revealed in the audit, which is heavily redacted for national security reasons. But as one indicator, 22 of the auditor’s 33 recommendations, as well as much of its analysis of the Department’s info-tech failings, are inked out of the document.
The audit’s blacked-out analysis comes nearly a year after an unprecedented “management alert” was issued by State’s Inspector General to warn that the department’s longstanding security failings could compromise not only “classified information vital to the preservation of national security in high-risk environments across the globe,” but the personal information on file concerning about 192 million American passport-holders.
The latest report also came out only three days after another Inspector General’s audit that highlighted “deficiencies” in the oversight work of one State Department Bureau that “allowed thousands" of unused email accounts to remain active in State’s system.
This posed “a significant risk for unauthorized access” not only to the unclassified email systems that have now apparently been under assault, but also apparently to State’s classified email accounts.
That document echoed the broader report of three days later in saying that repeated warnings since 2010 had noted “inadequate account and identity management controls” that increased the risk of outside hacking,
And while acknowledging some progress by the offending Bureau of Information Resource Management, or IRM, the auditors underlined that the bureau still had more than 44,000 email accounts more than its total of employees: 78,791. As the report wryly notes, the Inspector General’s office “concluded, and IRM concurred,” that at least some of the accounts, which constitute a security risk, weren’t needed.
(After the auditors arrived, the State Department’s Chief Information Officer, Steven Taylor, ordered a review of inactive email accounts, and removed and disabled about 5,000 of them.)
CLICK HERE FOR THE EMAIL AUDIT
State’s IRM bureau, whose work the Inspector General’s office has previous called “critical to the Department’s information security posture, has a painfully documented history of haplessness.
But there appears to be plenty of blame to go around.
Among other things, the latest report notes that of 17 State Department IT systems tested in the audit, seven, or more than 40 percent, did not have accompanying assessment reports tallying how effective their security controls were.
Moreover, State’s management of the protocols for remedying issues when identified, known ponderously as Plans of Action and Milestones, or POA&Ms, were “ineffective.”
As one measure of that inability to get things done, the auditors noted that of 29 critical findings from their previous year’s report on State’s deficiencies, none had found their way into the department’s overall POA&M database. That is because the people responsible for State’s various systems “did not consistently provide” such plants, nor did they “prioritize resources”—i.e., set aside money and manpower for them.
State’s explanation was that since “these vulnerabilities were expected to be closed within a short amount of time,” putting them in a database was “unnecessary.”
All that, of course, is supposed to change.
Among the uncensored recommendations in the latest info-tech audit are the notions that responsible State Department branches “adhere to completion dates for corrective actions,” and that the truant IRM bureau set time limits for other departmental branches to record “deficiencies” in the database devoted to fixing them.
The auditors also recommend that State’s Chief Information Officer and its top security officials make sure that “key information technology personnel with security responsibilities take specialized, role-based security training,” and that compliance with the training programs be tracked.
Both are things that the State Department is already supposed to do under various government-wide guidelines, and both were also recommended, apparently with insufficient effect, a year ago.
Concludes Steven Bucci, director of a foreign and national security policy center at the conservative Heritage Foundation: “Clearly the State Department has not taken cybersecurity seriously. Congress should be asking a lot of questions of the senior leaders, past and present, of State and they should be doing it now.”
However, when asked questions by Fox News about the “significant deficiency” designation of its information security status, the large number of inactive email accounts in its system, and its plans for corrective action, the State Department declined to comment.
Before that, a State Department spokesman said, among other things, that the Fox News questions had gotten lost for two days due to State’s email shutdown as a result of external hacking attempts.
George Russell is editor-at-large of Fox News and can be found on Twitter: @GeorgeRussell or on Facebook.com/George Russell







































